Acknowledgement, Circulation, Obscurity, System Ambience
Dragan Espenschied | Tue Jun 24th, 9:30 a.m.
Cultural value in the digital realm is usually conferred in one of two ways—by the imprimatur of an established gatekeeper,1 or by the approval of digital mass media users.2
In the absence of either of the above, a third value emerges: obscurity. Not to be confused with artificial scarcity or exclusivity,3 digital obscurity offers the experience of encountering something that has gone unseen or unnoticed by others. It is a rare, intimate and personal moment in a media world that is geared toward high visibility and high-speed circulation. Discovering a web site where the traffic counter shows a single-digit number is so attractive because the counter proves that you, the viewer, are part of a small and select group to have experienced a particular digital artifact or practice.
Just as encountering something obscure can be very personal and poetic, the act of posting about it can be quite vulgar, as it deprives others from finding it for themselves or having the illusion of being the only one. So, it is with mixed feelings that I share with you the following truly obscure digital artefact.
Bomb Iraq 
In 2005, Cory Arcangel bought a used computer at a Salvation Army store in Buffalo, New York. Originally he was attracted to it because of its rarity: the Macintosh TV was a rather badly designed, half-hearted hybrid of a Macintosh Computer and a TV set, that performed neither of its designated functions very well and lacked any cool things that might come from the synergy. The machine was a commercial flop, only around 10,000 units were produced during a few months between 1993 and 1994.
It became apparent that the computer was previously owned by a family and mainly used by their teenage son for school assignments and games. There was so much stuff to find.
Peeking through all the folders, in between some calculator programming and homework, Cory stumbled upon a simplistic, homemade computer game called Bomb Iraq.
There is not much one can do in the game except flip through a virtual deck of cards depicting a hand-drawn missile hitting a clipart map outline of Iraq. It is a pretty decent find, brutal and casual, its strongest point is the visual ambiguity of the “home” icon depicted as a house with the bomb missile looming above. It is likely that until Cory found the computer, this software was never witnessed before by anybody except the computer’s owner. In the 2005 show Breaking and Entering: Art and the Video Game at the Pace Wildenstein Gallery in New York, Cory exhibited Bomb Iraq as a readymade. Unfortunately the computer’s hardware died three days into the exhibition.
![]() Using the services of computer pros, Cory had the hard disk’s contents rescued to a CD and continued showing Bomb Iraq on a contemporary laptop computer for the show. However, Apple soon phased out support for their “Classic” operating system, so it became too technically difficult to display this work in a meaningful way.
Using the services of computer pros, Cory had the hard disk’s contents rescued to a CD and continued showing Bomb Iraq on a contemporary laptop computer for the show. However, Apple soon phased out support for their “Classic” operating system, so it became too technically difficult to display this work in a meaningful way.
 System Ambience
System Ambience
Today, Emulation as a Service4 can bring the broken Macintosh TV back to life, for a new audience. As a fan of the original 2005 objet trouvé, and as Rhizome’s Digital Conservator, I suggested to Cory that I restore it and make it public.
In the restoration process, some tender aspects of the artifact could be uncovered. Bomb Iraq performs best when embedded in its full context—which emulation is able to almost fully capture. While most users will be happy simply to experience Bomb Iraq, the whole system is there to explore. Cory and I worked to remove all the files that could identify the computer’s original owner, moving the focus to an afterglow of this person, drive-by inscriptions in the system’s configuration.
Letters, photos and some game high score entries bearing the owner’s full name had to be deleted, but the arrangement of icons, the software installed , the modified system font and desktop background—which all once made sense to somebody—demonstrate the narrative power of system ambience.5
Then I found this note: 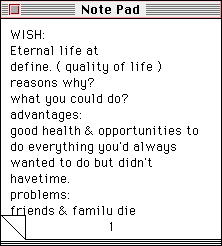
Cory and I both agreed that this note was probably better than the actual centerpiece of the work, Bomb Iraq. When I sent him this screenshot, he replied:
OMGssss!!!!!! This should be the new title!~~~~~~
I encourage you look for this note, and other things.
How to do it
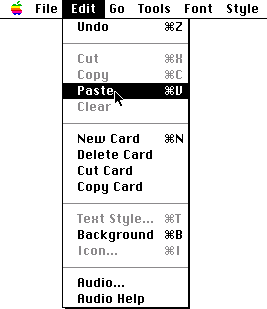
Maybe you have never used a Macintosh from the 1990’s. Here is how it works:
To activate a menu item, move the mouse pointer to a menu entry like “File,” then press and hold down the mouse button to bring up all options. While holding the mouse button down, move the cursor to the option you want to activate and release the mouse button.
This is the icon for the computer’s hard disk:![]()
Double-click the icon to open up a “Finder” file manager window. Any folder icons inside this window can be double-clicked again to reveal their contents. Scroll around in these windows as the icons you are looking for might be not visible in the original view.
The rest I’m sure you will be able to figure out.
Examples might be the 1997 documenta X art festival dedicating space and infrastructure to the net.art movement, giving it institutional blessing as actual art, or the MoMA’s 2012 acquisition of a few selected video games, granting the whole genre access to the world of design. On a more mundane level, inclusion into the AppStore or GooglePlay signifies the value of software.
SMS speak, popular GIF animations that have been copied over and over again, a cat video that went viral, a certain practice like Caging Facebook profiles: if something is repeated millions of times, there is no way of ignoring its cultural influence.
Attempts to artificially create a “limited resource” on the internet have not been met with much enthusiasm. For example, the artist-run website and domain hell.com already in 1999 restricted access to their material, trying to evoke a mysterious and conspirative setting—only to have it copied and distributed on the first possible occassion.
also known as bwFLA, a hosted framework that allows users to access and use legacy operating systems in their browser, developed at the University of Freiburg
You might wonder if it is okay to look around on somebody else’s computer like that. Be assured that this computer was last used by the original owner in November 2000, to install a driver software, probably for getting files off of it. This computer was never connected to the Internet, it never contained any kind of conversation, a history of visited websites or search terms. The very few files that would reveal anything about the owner’s identity have been removed. And visitors of the 2005 exhibition have already discovered nice things besides Bomb Iraq.


